Data breaches are on the rise and healthcare is not immune, says Michelle Caswell, JD, Senior Director of Legal and Compliance for Clearwater Compliance LLC. Healthcare organizations hear about the vulnerability of protected health information, but don't do much more than hope that they won't be the next target.
"Cyber-attacks are not going away," Michelle says. "It is time that healthcare organizations start becoming proactive in their compliance and security measures instead of reactive in response to a data breach."
Michelle and the team at Clearwater work to help these organizations and their service providers improve patient safety and the quality of care by assisting them in establishing, operationalizing and maturing their information privacy and security compliance and risk management programs. They provide comprehensive, by-the-regulations compliance software and tools, risk management solutions, education and training, and professional services for organizations needing to understand where their compliance gaps and security risks are and what steps they can take to address them.
Here, Michelle gives us an overview of the most common problems she observes with data security, and offers insight on how practices can stay ahead of compliance issues.
What are the most common weak spots you observe in healthcare providers when it comes to data security?
One of the most common weak spots for health care providers, and most organizations in general, is the consistent failure to conduct a thorough risk assessment on every information asset used to create, receive, maintain or transmit protected health information (PHI). This also includes any other sensitive data (for example, credit card data, employee files, or financial statements). A risk assessment is required by the HIPAA Security Rule, Meaningful Use, PCI DSS and many other data security regulations because it sets the framework for an organization's entire information risk management program, which is fundamental to compliance.
What are the worst-case scenarios for healthcare providers that do not do enough to safeguard their data?
Many regulatory agencies have jurisdiction over health care providers. Most health care providers have heard that the U.S. Department of Health and Human Services (HHS) Office for Civil Rights (OCR) has the ability to impose hefty civil money penalties against covered entities and their business associates. However, most health care providers do not realize that not safeguarding healthcare data can bring other regulatory agencies to investigate compliance. OCR refers cases that require criminal investigations to the Department of Justice.
The FTC has jurisdiction over health care providers if that health care provider is engaged in unfair and deceptive trade practices (for example, advertising that patient data is secure, yet not taking the appropriate steps to ensure security). Even state attorneys general can file HIPAA enforcement actions on behalf of the people of their state.
Data breaches in the global healthcare sector accounted for 65 percent of all identities breached in 2012, according to Symantec's Internet Security Threat Report. By not safeguarding data, health care providers are opening their entire HIPAA compliance program, or lack thereof, to multiple regulatory enforcement agencies.
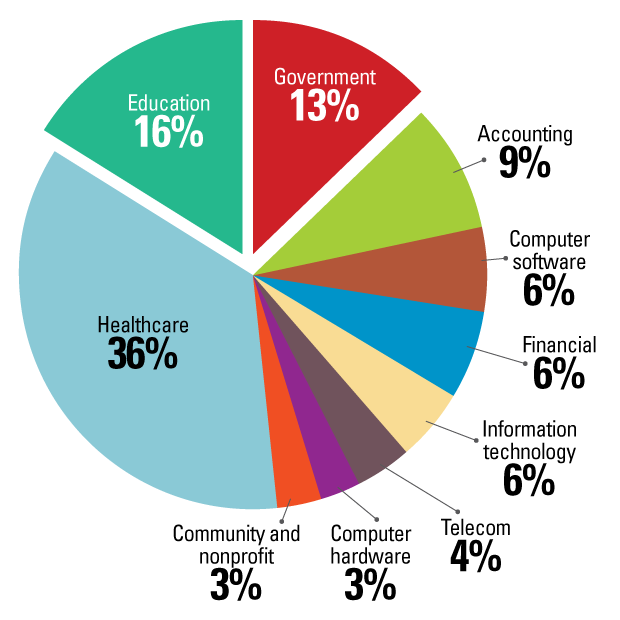 Source: Symantec
Source: Symantec
What are healthcare providers' biggest frustrations or complaints when it comes to data security?
A common complaint among health care providers is that data security prevents them from providing patient care quickly and efficiently. For example, in order to protect improper access to an electronic health record (EHR), the information technology department sets the password complexity to eight characters, with a combination of upper and lowercase. It is typical for a physician to request that she or he does not have to comply with the password complexity, citing that it directly impacts patient care.
What should providers be doing to stay ahead of compliance changes?
There are many organizations out there dedicated to health care compliance. Even if you are not a compliance officer, it would be a great idea to join one of these organizations as they typically send weekly news updates, host conferences and provide informational webinars. These are great ways to stay ahead of changes.
Why is training such a critical component of compliance?
Although cyber security breaches seem to be the only ones making headlines, employees are still the root cause of impermissible uses and disclosures of PHI. Some employees have malicious intent when impermissibly using or disclosing PHI; however, most employees simply do not understand what is required of them. By failing to train employees on the importance of safeguarding sensitive information, an organization cannot expect its employees to safeguard that information. Regardless of compliance, training the workforce in security awareness just makes good business sense.
What should organizations be doing to better train their employees?
First of all, it is important to recognize that any individual having access to PHI on behalf of an organization should receive this training. HIPAA defines the term "workforce" as full-time employees, part-time employees, contractors, and volunteers. The entire workforce should be trained.
Secondly, organizations need to move beyond training their workforce solely on what is required by regulations, and instead make the training relevant to their organization and to the specific role of each member of their workforce, with the overall goal of protecting sensitive data. It isn't "once and done," but a sustained awareness and training program, including updates when new threats emerge.
Remember, it's an organization's workforce members that are the first line of defense when it comes to protecting sensitive data. Train the workforce on their responsibility to protect sensitive data and what steps they can take to protect sensitive data. Keep training relevant, up-to-date, sustained and tailored to an organization's own policies and procedures.
What advice do you find yourself repeating to clients over and over?
The biggest piece of advice that we find ourselves repeating is that in order to keep your data secure, you must conduct a complete risk assessment. It is a critical step to information security and risk management.
Once you find what your risks are, then you must be deliberate in doing something about them! A risk assessment is not a document that sits on a shelf somewhere once you have completed it; it should be a roadmap to guide the organization's response to the risks identified.
The classic response choices to risks are to accept them, avoid them, and mitigate them by implementing improved controls or transfering the risk to a third party. But ignoring them is not OK and opens the organization up to enforcement action, potential data breaches and thus financial and reputational harm.

Michelle is the Senior Director of Legal/Compliance with Clearwater Compliance.
Connect with Clearwater on Facebook, Twitter and LinkedIn.