NOTICE: eCW Server Vulnerability Discovered
This morning eClinicalWorks notified us of an urgent update required for self-hosted clients. The update
regards a vulnerability that was discovered in the Apache “Log4J 2” utility as published by the Apache
Software Foundation. This software is a dependency upon which eClinicalWorks relies, so it is
imperative that this be patched immediately to prevent unauthorized code execution on your server.
For self-hosted eClinicalWorks servers, please ask your server administrator to run the APU Tool to
accept patch A-14610. If you are hosted on Linux, please contact eClinicalWorks for patch installation
services. eClinicalWorks Cloud clients do not need to take any action, remediation measures are already in progress. For PSM hosted clients, the patch installation and further remediation measures have been completed. For self-hosted clients whose eCW servers are managed by Revele, we will be contacting you directly to install this patch soon. If Revele has been granted unattended access to your server, we will be completing this update behind the scenes and nothing will need to be done on your end.
UPDATE: eCW has rolled out a comprehensive follow-up patch A-14666 for the Log4J vulnerability. This patch is comprehensive, so if you have not yet applied Patch A-14610 there is no need to apply it. Patch A-14666 should be installed on all servers to mitigate the issues found in the Apache Log4J library.
The full patch announcement follows.
Patch ID A-14666 is now available for download
Patch A-14610 was released earlier towards mitigation of this vulnerability CVE-2021-44228. Based on
newer information available, this patch is an update on top of patch A-14610. This patch should be
taken, even if you have applied the earlier patch.
Log4j Upgrade
Patch ID A-14610 is now available for download
Dear eClinicalWorks Customer,
eClinicalWorks is constantly reviewing technology platforms, architecture, and security to provide the
best possible solutions to its clients. As a result, eCW is sharing a critical vulnerability notification, CVE-
2021-44228, which impacts multiple versions of the Apache Log4J 2 utility as published by the Apache
Software Foundation on December 10th, 2021. For more information, please refer
to https://nvd.nist.gov/vuln/detail/CVE-2021-44228
This vulnerability allows for unauthenticated remote code execution. log4J 2 is an open-source java
logging library developed by the Apache Software Foundation. Log4J 2 is widely used in many
applications and is present as a dependency.
eClinicalWorks is impacted by this CRITICAL vulnerability and is taking the necessary steps to mitigate
the issue based on information published by the Apache Software Foundation.
For customers on the eCW cloud, no action is necessary. eCW is taking the necessary steps to apply
mitigation on the eCW cloud hosted practices.
For more information, please refer to the notification posted on the Customer Portal
at my.eclinicalworks.com titled eCW Security Vulnerability Update - Apache Log4J - Dec 2021. As more
information related to the vulnerability becomes available from Apache Software Foundation, this
notification may receive further updates. The customers should look for these updates on the Customer
Portal: my.eclinicalworks.com
Locally hosted customers should also set the log4j2.formatMsgNoLookups parameter to true when
starting the java virtual machine. The technical instructions for making this change are part of the
notification on the customer care portal: eCW Security Vulnerability Update - Apache Log4J - Dec 2021
----------------------------------------------------------------------
Self-Hosted Customers: Please accept this patch A-14610 by running the APU Tool.
Linux Customers: please contact eClinicalWorks to schedule this update.
If you are hosted on eClinicalWorks Cloud - no action is necessary.
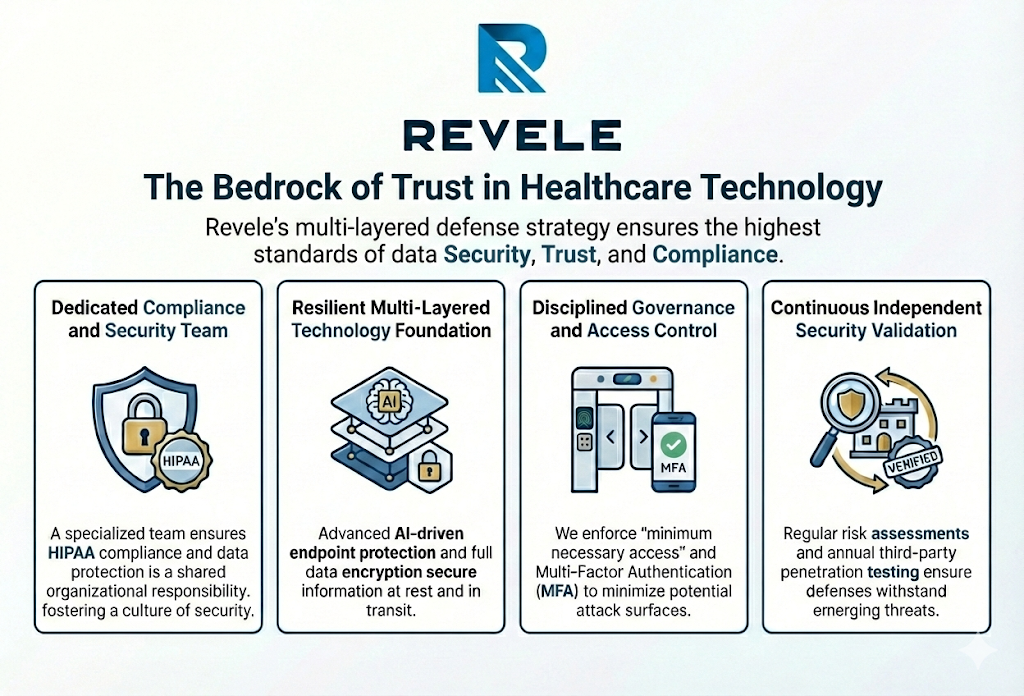
end-to-end rcm solution
Demand more from your revenue cycle.
Our integrated solution brings together robust data, intelligent claim handling, and performance consulting to guarantee a 10% increase in cash flow.